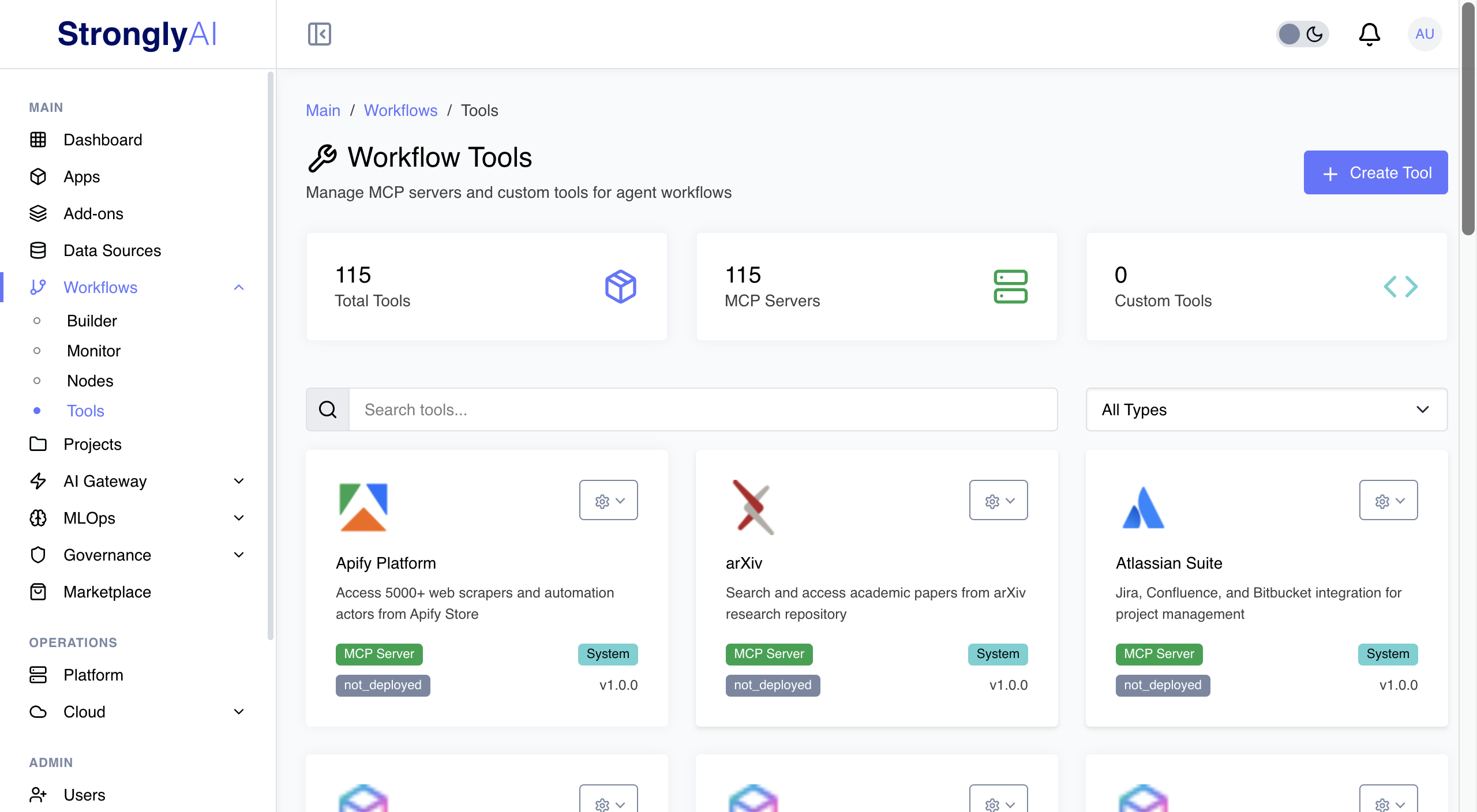
100+ MCP Servers. Zero Static Credentials.
Enterprise MCP with multi-tenancy, JIT credentials, and fine-grained access control. Runs inside your perimeter. No API keys in config files. Ever.
MCP for Production. Not Prototypes.
Security-hardened, multi-tenant, auto-scaling MCP infrastructure that runs in your environment
100+ Certified MCP Servers
GitHub, Slack, PostgreSQL, MongoDB, Stripe, and more. Each server containerized, security-hardened, running in isolated Kubernetes pods. Not npm packages on your laptop.
Multi-Tenancy
One server instance, hundreds of users, complete isolation. Each user hits their own resources with their own credentials. Efficient infrastructure without security shortcuts.
Just-in-Time Credentials
Short-lived tokens replace static API keys. Scoped to minimum permissions. Revoked after use. Never persisted. If an attacker gets in, they find nothing.
Fine-Grained Access Control
Workflow-level permissions, user isolation, RBAC, resource-level controls. Define who accesses what, when, and how. No broad permissions. No "just make it admin."
Internal Hosting
Kubernetes pods inside your VPC, private cloud, or on-prem. Data never leaves your network. Compliance and data sovereignty by architecture, not by policy.
Cloneable & Customizable
Clone any server. Customize for your needs. Stored in isolated S3 directories with full versioning and audit trails. Fork, do not rewrite.
Drag-and-Drop Integration
Drag MCP servers into workflows. Connect to AI models, data transforms, and business logic. No glue code. No integration sprints.
Auto-Scaling
Kubernetes scales MCP servers on demand. Handle spikes without over-provisioning. Scale down when idle. Infrastructure that matches your load curve.
Complete Audit Trails
Every interaction logged and monitored. Credential usage, data access, operations - all tracked. Build, deploy, and runtime logs for compliance and debugging.
The MCP Security Problem. Solved.
Most MCP deployments are a security risk. Ours are not.
Zero Exposed API Keys
JIT credentials mean nothing valuable sits in config files. Compromise a system, find nothing. That is the correct security posture.
One Server. Hundreds of Users.
Multi-tenancy eliminates per-user deployments. Efficient resource utilization with complete security isolation. Lower cost, same guarantees.
HIPAA. PCI-DSS. SOC 2. Ready.
Internal hosting, data sovereignty, audit trails, fine-grained access control. Built for regulated industries. Not bolted on after an audit finding.
Enterprise MCP. Production-Ready.
An FDE will scope your MCP architecture, security requirements, and integration points.